
AI CERTS
5 hours ago
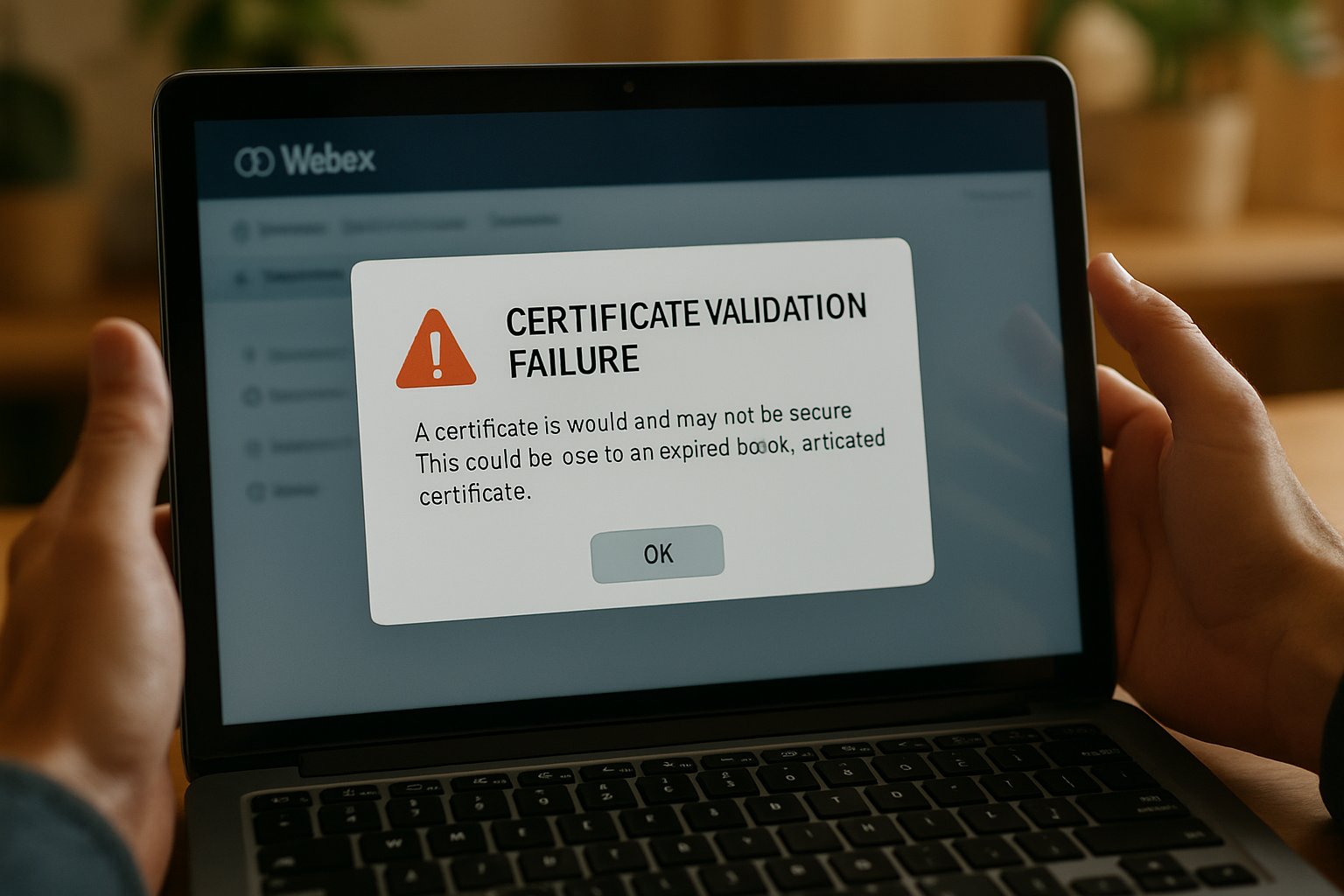
AI Software Security Lessons from Cisco Webex Certificate Flaw
Cisco patched the weakness server-side, requiring no user update. Moreover, the company published a detailed advisory clarifying risk boundaries and mitigation status. Nevertheless, security leads demanded deeper analysis of cert handling in distributed meeting flows. This article dissects the flaw, contextualizes related 2025 collaboration issues, and outlines forward-looking defenses.
Readers will gain a clear view of exploitation prerequisites and real-world impact. Additionally, we compare this cert issue with April’s high-severity remote code execution bug. In contrast, today’s flaw affects confidentiality more than system integrity. Finally, the discussion maps recommended controls and relevant certifications that bolster expert readiness.
Flaw Overview And Impact
CVE-2025-20215 resides in the Webex meeting-join handshake. Therefore, improper certificate validation enabled session hijack under specific timing windows. The defect maps to CWE-295, confirming inadequate certificate authenticity checks. From an AI Software Security standpoint, any trust failure in identity negotiation undermines automated policy engines.
Cisco rated the Vulnerability with a CVSS score of 5.4, labeling impact medium. However, confidentiality loss can be acute when sensitive boards convene remotely. Attackers joining as trusted employees could watch presentations or capture shared documents silently. Integrity and availability rated lower because the flaw neither alters data nor crashes services.
Meanwhile, exploitation demands proximity on the same Wi-Fi or wired segment. Consequently, large-scale internet campaigns remain unlikely, though insider threats grow. These impact nuances guide prioritization decisions for overextended security teams. Nonetheless, the episode underscores continuous cert monitoring as a baseline duty.
The flaw threatens privacy when local networks are untrusted. However, strict conditions temper widespread panic and signal measured response priorities. With scope clarified, we now examine exactly how attackers must position themselves.
Attack Prerequisites In Focus
Successful exploitation rests on three cumulative factors. First, the attacker must share an adjacent network with the target. Second, they need capability to observe and interrupt encrypted join traffic in real time. Finally, precise timing is required to inject forged cert responses before back-end validation concludes.
Moreover, user interaction still occurs because meeting invites trigger the original join. In contrast to remote code execution bugs, no malicious link alone suffices. Researchers from TU Darmstadt and partners confirmed these barriers during coordinated disclosure to Cisco. Therefore, the Vulnerability earns a high attack complexity flag inside scoring templates.
These constraints narrow threat actors to insiders, conference-center snoops, or café intruders sporting packet tools. Consequently, executive travel and hybrid events remain focal points for defensive monitoring. Such context frames risk tolerance before patch cycles overwhelm roadmaps. Attackers face steep hurdles, yet motivated insiders might persist.
Next, we explore how Cisco neutralized that possibility without client updates.
Cisco's Swift Cloud Fix
Cisco implemented a server-side block within Webex Meetings’ authentication gateway. Subsequently, forged cert chains are rejected before user sessions finalize. The vendor announced the move in its public Advisory on 6 August 2025. No desktop or mobile patch became necessary, reducing operational friction dramatically.
Moreover, Cisco's status portal showed zero customer reports of exploitation before remediation. Nevertheless, the company encouraged administrators to review meeting access logs for anomalous join patterns. Such transparency aligns with evolving AI Software Security governance models demanding evidence-based trust. Therefore, the company preserved confidence while avoiding platform downtime.
Industry analysts praised the rapid fix cadence, especially when contrasted against slower on-premises collaboration suites. However, they urged ongoing penetration testing of cert logic to preempt regressions. These suggestions echo across quarterly webcast briefings with Webex enterprise customers.
Cisco delivered a clean, cloud-level correction and communicated openly. The next section contrasts this episode with April’s more severe Webex bug.
Comparing 2025 Webex Bugs
April 2025 witnessed CVE-2025-20236, a high-severity remote code execution flaw triggered by crafted meeting links. In contrast, CVE-2025-20215 targeted the join flow and required adjacency. Consequently, security teams triaged the earlier bug first despite simultaneous media coverage. Both disclosures emerged through Cisco's Advisory mechanism, providing consistent guidance formatting.
Moreover, the April incident demanded endpoint upgrades, forcing administrators to coordinate device rollout windows. The Vulnerability avoided that pain because cloud services updated transparently. Nevertheless, multiple Webex advisories within months intensified board-level scrutiny over collaboration risk. Therefore, mature programs integrated Webex findings into broader AI Software Security scorecards.
- RCE bug demanded client patches; cert issue did not.
- Earlier flaw scored 8.8 CVSS; August flaw scored 5.4.
- Both bugs surfaced through Cisco Advisory channels, streamlining communications.
- Adjacency requirement limited scale of cert attack vectors.
The comparison underscores that not all Webex bugs carry equal urgency. However, consistent diligence remains vital as attack surfaces evolve. With context established, let us assess enterprise risk profiles.
Operational Risk For Enterprises
Enterprise exposure hinges on workforce mobility and meeting culture. Organizations relying on public Wi-Fi present richer targets. Consequently, zero-trust access policies and VPN enforcement reduce cert hijack chances. AI Software Security dashboards should flag unusual join patterns for analyst review.
Security leaders polled in September 2025 reported moderate concern yet minimal remediation cost. Furthermore, many already restricted meeting attendance to enrolled corporate identities. Those controls mirror guidance from the vendor Advisory and national CERT bulletins. Nevertheless, analysts warned that complacency may grow as cloud vendors absorb patch duties.
Automated trust decisions must still be validated regularly by penetration tests. Therefore, red teams should attempt local-network impersonation during annual exercises. These simulations feed AI Software Security models with fresh adversarial data.
Enterprises remain largely safe, yet proactive monitoring sustains resilience. Next, we outline concrete defensive measures recommended by experts.
Best Defensive Practices Now
Experts agree on layered mitigations that cost little. First, enforce corporate VPN for external meeting joins wherever feasible. Second, segment guest Wi-Fi from internal traffic, limiting lateral observation of TLS exchanges. Furthermore, enable Webex lobby features to approve each participant manually in high-risk sessions.
Organizations should also activate alerting for concurrent logins under identical user identifiers. Moreover, AI Software Security analytics can blend join metadata with contextual device scores. Such fusion quickly exposes anomalies before sensitive material leaves screening. Regular training reminds travelers to avoid unencrypted hotspots when accessing collaboration services.
- Review vendor Advisory updates weekly for emerging Webex patches.
- Document certificate pinning expectations inside internal security baselines.
- Schedule tabletop drills simulating adjacent-network adversaries.
These measures fortify daily operations against adjacent network threats. However, career advancement demands formal validation of these AI Software Security competencies. Accordingly, professionals seek accredited pathways to demonstrate network defense mastery.
Certifications And Next Steps
Security talent shortages amplify the value of specialized credentials. Consequently, hiring managers prioritize candidates who understand cert chains inside collaboration stacks. Professionals can deepen expertise with the AI Network Security™ certification. The course emphasizes AI Software Security concepts, PKI fundamentals, and live traffic inspection labs.
Moreover, the curriculum includes case studies covering Cisco Webex and other SaaS platforms. Graduates gain playbooks for responding to Vulnerability disclosures within hours. Therefore, organizations investing in staff training build resilience beyond single Advisory events. Meanwhile, practitioners should subscribe to trusted mailing lists and monitor CVE feeds.
These proactive steps keep AI Software Security maturity aligned with evolving collaboration landscapes. We now recap the essential insights and actions.
In summary, CVE-2025-20215 exemplifies how cert oversights threaten remote collaboration privacy. However, Cisco's rapid, cloud-based fix reduced disruption and highlighted service agility benefits. Enterprises remain safe when layered defenses, vigilant logging, and dynamic AI Software Security analytics converge. Moreover, comparing collaboration bugs underscored the need for nuanced risk scoring rather than blanket urgency. Future readiness grows when professionals pursue credentials like the AI Network Security™ certification.
Act now by reviewing your meeting controls and exploring the linked training to safeguard tomorrow's conversations. Consequently, organizations that integrate skills, policies, and cloud partnership will navigate future cert threats with confidence. Stay informed, stay certified, and keep meetings protected.



