
AI CERTS
2 hours ago
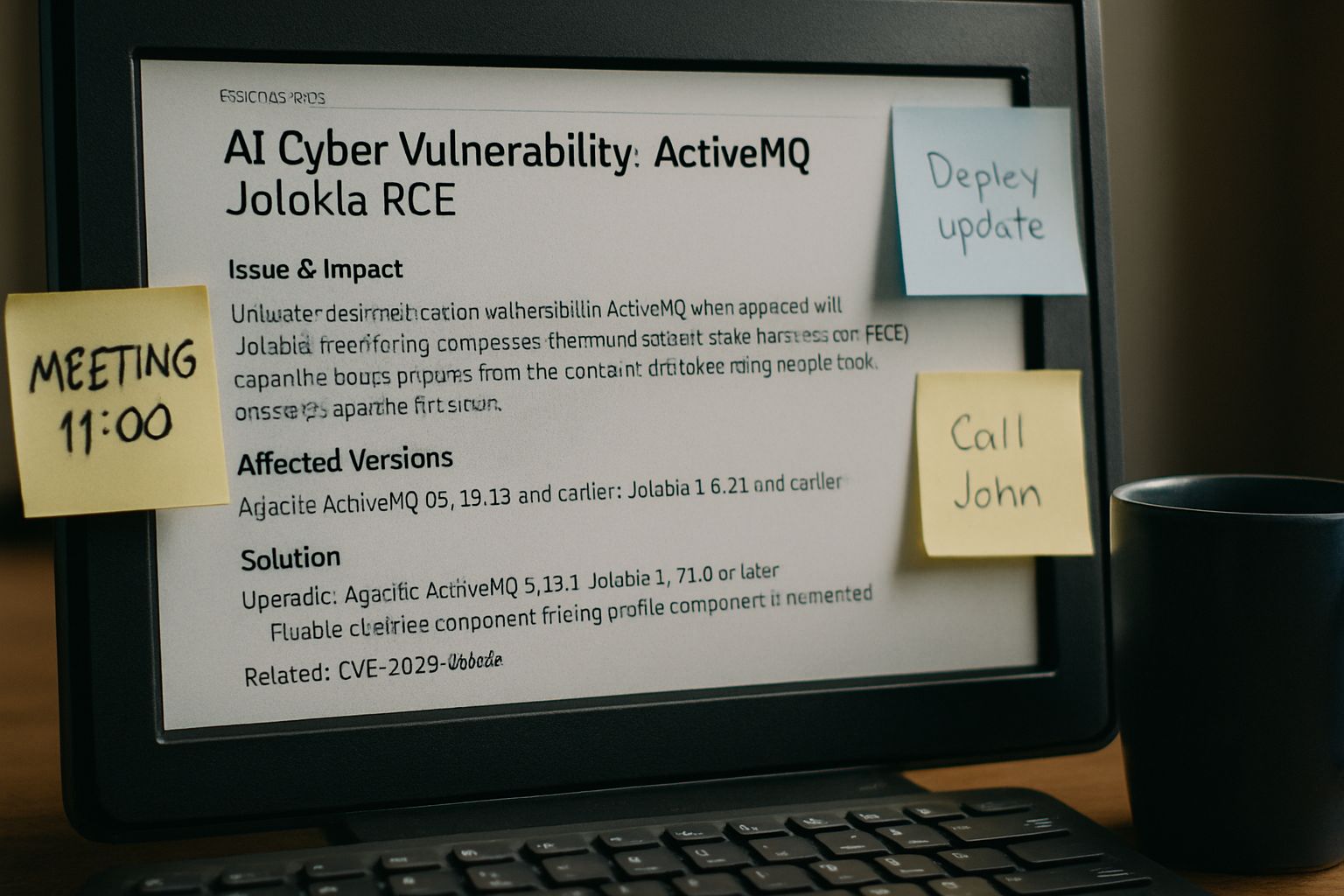
AI Cyber Vulnerability: ActiveMQ Jolokia RCE Exploitation Surges
This unfolding scenario exemplifies an AI Cyber Vulnerability that blends automation, cloud reach, and open-source risk.
Furthermore, public proof-of-concept exploit code now sits on GitHub, lowering barriers for threat actors.
Security leaders must act decisively, or operational messaging infrastructure may become adversary beachheads.
The following report examines timeline, exploit flow, detection, and strategic lessons.
Evolving AI Cyber Vulnerability
Initially, Horizon3.ai discovered the flaw and alerted Apache on 22 March 2026.
Apache shipped fixes within nine days, releasing versions 6.2.3 and 5.19.4 to the community.
However, public disclosure in early April triggered mass scanning within hours.
Subsequently, CISA added the flaw to its Known Exploited Vulnerabilities catalog on 16 April.
Consequently, federal agencies face a binding 30 April patch deadline under BOD 22-01.
In summary, disclosure rapidly shifted the issue from private report to global emergency.
Therefore, understanding the underlying mechanics becomes critical for defenders.
Technical Root Cause Analysis
This AI Cyber Vulnerability centers on the Jolokia JMX-over-HTTP bridge embedded in the ActiveMQ web console.
Moreover, historical configurations allowed authenticated exec operations on several broker MBeans.
Attackers abuse the addNetworkConnector method with a crafted discovery URI referencing remote Spring XML.
Because Spring instantiates beans before broker validation, malicious code executes inside the Java process.
Therefore, remote attackers gain full RCE privileges, matching root equivalent permissions on many Linux hosts.
These mechanics reveal an architectural weakness spanning more than a decade of releases.
Consequently, exploit chain specifics warrant deeper inspection next.
Complete Exploit Chain Details
This AI Cyber Vulnerability unfolds through a compact three-step sequence.
First, the attacker authenticates or leverages misconfigured anonymous Jolokia access.
Second, they submit an addNetworkConnector call carrying a vm:// brokerConfig that references evil script XML.
Third, Spring fetches the external XML, instantiates a bean, and executes attacker commands, achieving reliable RCE.
Shadowserver telemetry shows thousands of connection attempts following the above sequence since mid April.
- Install crypto-miners for immediate profit
- Establish reverse shells for persistence
- Pivot into adjacent cloud workloads
Overall, the chain is simple, reliable, and now automated within multiple public scripts.
Meanwhile, exposure statistics illustrate the urgency of patching.
Global Exposure Statistics Overview
According to Shadowserver, 6,000–7,500 brokers answered scans during late April.
In contrast, that figure barely dropped after the Apache advisory, indicating slow defender response.
BleepingComputer reports fresh infection attempts every few minutes, based on honeypot telemetry.
Therefore, internet-facing instances remain high-value targets until network filters or upgrades are applied.
- Estimated vulnerable brokers: ~7,000
- CVSS 3.x score: 8.8 (High)
- CISA remediation deadline: 30 April 2026
These statistics expose the wide blast radius carried by this AI Cyber Vulnerability.
Consequently, immediate mitigations become mandatory, as the next section explains.
Urgent Mitigation Steps Required
Administrators should upgrade to ActiveMQ Classic 5.19.4 or 6.2.3 without delay.
Alternatively, block external access to the web console and Jolokia endpoints until maintenance windows arrive.
Furthermore, enforce strong credentials because weak defaults convert an authenticated flaw into unauthenticated RCE.
Apache advisories also recommend disabling JVM deserialize features and restricting connector whitelists.
Professionals can enhance their expertise with the AI+ UX Designer™ certification.
Collectively, these measures shut the main doors exploited today by the AI Cyber Vulnerability.
However, detection remains vital because some breaches have already occurred.
Detection And Response Guidance
Security teams should enable verbose access logging on Jolokia and the console.
Additionally, search for vm:// strings containing brokerConfig=xbean, especially within POST bodies, to spot potential RCE.
Moreover, monitor the ActiveMQ Java process for unexpected child shells or outbound HTTP pulls.
SIEM queries can map such events to MITRE ATT&CK T1059 or T1105 techniques for enrichment.
- addNetworkConnector calls in logs
- Outbound fetch to attacker URL
- New process spawned by java.exe
Effective monitoring provides a last safety net when patching lags.
Therefore, lessons learned here influence broader defensive strategies against every AI Cyber Vulnerability.
Key Strategic Security Takeaways
First, middleware platforms deserve the same rigorous hardening as perimeter gateways.
Second, rapid disclosure plus public PoC accelerates attack tempo, shrinking defender response windows.
Third, inventory accuracy determines whether organizations even notice hidden brokers needing updates.
Moreover, combining patch management with continuous detection offers layered assurance against future variants.
Finally, each AI Cyber Vulnerability underscores the importance of cross-disciplinary skills between DevOps and security.
These takeaways equip leaders to refine governance and budget priorities.
Consequently, the following conclusion consolidates urgent next actions.
The ActiveMQ Jolokia flaw exemplifies how routine components can produce enterprise-wide crisis moments.
Nevertheless, fast vendor response and clear advisories supply defenders with workable fixes.
Organizations that upgrade, lock down endpoints, and monitor logs will likely avoid long-term damage.
Meanwhile, threat actors continue probing unpatched brokers using automated exploit kits.
Therefore, leadership should treat this AI Cyber Vulnerability as a board-level risk metric.
Moreover, deeper staff development strengthens organizational resilience against future incidents.
Act now: patch systems, review logs, and pursue advanced certifications to stay ahead of every AI Cyber Vulnerability wave.
Disclaimer: Some content may be AI-generated or assisted and is provided ‘as is’ for informational purposes only, without warranties of accuracy or completeness, and does not imply endorsement or affiliation.



