
AI CERTS
2 hours ago
Agent Security Brief: Navigating the OpenClaw Root Exploit Crisis
Moreover, regulators and vendors already publish strict guidance that shifts how organizations treat agent workloads. Meanwhile, adversaries automate exploit delivery using malicious marketplace skills and drive-by browser scripts. Therefore, understanding root causes alongside mitigations becomes vital before enabling autonomous tooling on production machines. Nevertheless, rapid patch adoption paired with disciplined identity isolation can still keep experimentation safe.
OpenClaw Threat Landscape Overview
Security researchers classify OpenClaw as a high-risk local runtime because it holds tokens and executes code. Moreover, default installs bind the gateway on localhost without strict origin checks, inviting cross-context abuse. In contrast, earlier agent frameworks often limited shell privileges, reducing blast radius when an exploit landed. SentinelOne notes that compromised agents frequently pivot, dropping payloads that run with root permissions when configured insecurely. These dynamics help explain strong concern within the Agent Security community.
OpenClaw’s architecture grants powerful capabilities and equal risk. Consequently, tracking each exploit is essential; the next section details the timeline.
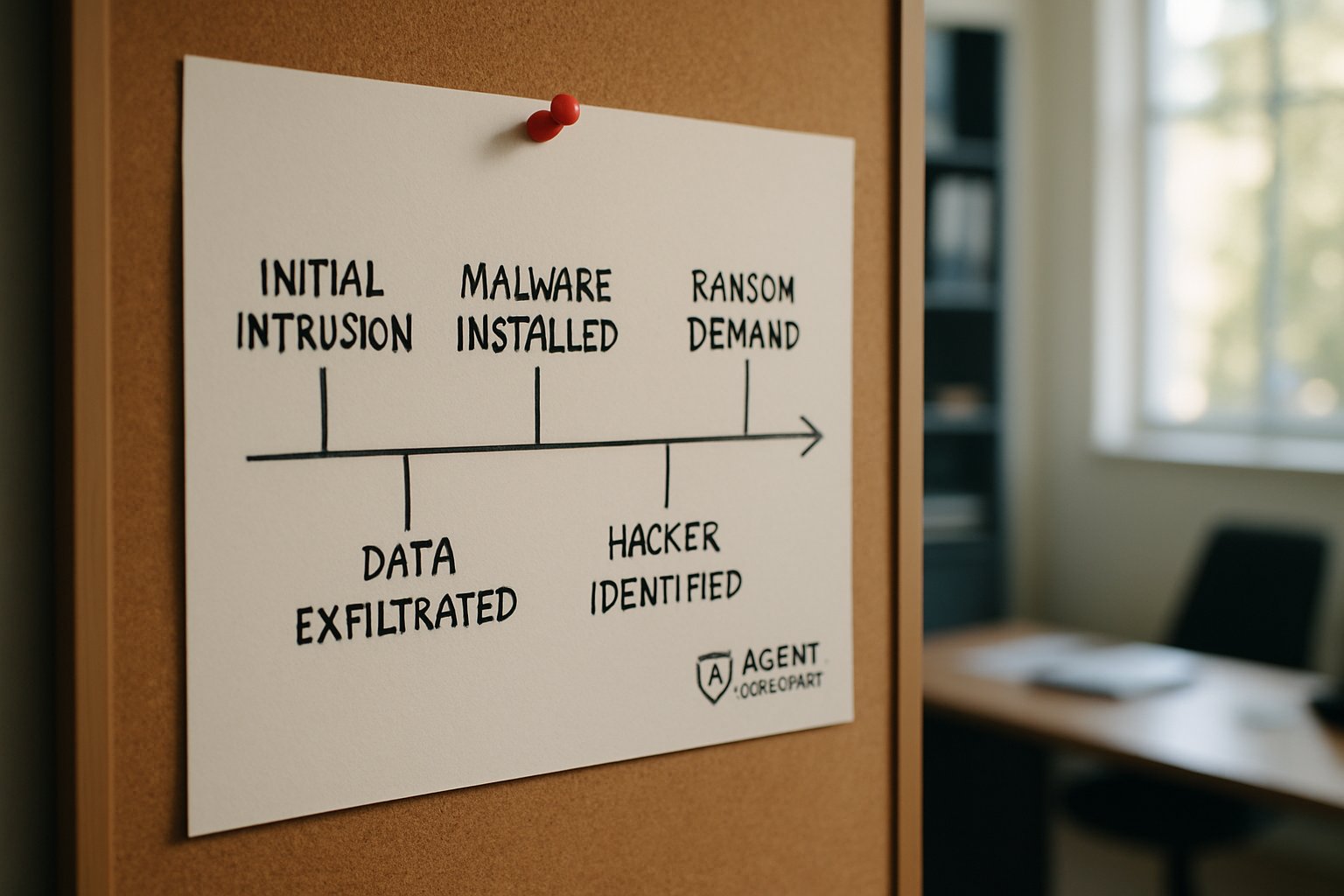
Recent Exploit Timeline Highlights
February through April generated a rapid series of disclosures, patches, and public proof-of-concept code. Furthermore, CVE-2026-25253 demonstrated one-click exploit enabling token exfiltration via WebSocket hijack. Meanwhile, CVE-2026-32056 allowed command injection by poisoning shell startup variables.
- 954 gateways remained internet-reachable during a late-2025 McAfee scan.
- Illumio observed more than 4,500 misconfigured installations in early 2026.
- Researchers discovered 341 malicious marketplace skills during a single March sweep.
- Multiple advisories pushed three major patch branches within eight weeks.
Consequently, administrators struggled to track patch cadence, leaving lagging nodes exposed. These numbers clarify why Agent Security teams emphasize continuous inventory and rapid update pipelines.
The timeline shows relentless attacker curiosity and defender fatigue. Subsequently, understanding root shell pathways becomes the logical next focus.
Root Shell Attack Pathways
Adversaries chase root shells because full privileges simplify lateral movement and persistence. However, two primary attack paths dominate current incident reports. First, a malicious webpage captures tokens, then issues system.run calls that launch a shell with unsanitized variables. Moreover, by redirecting HOME to a crafted directory, the attacker injects commands before any allowlist executes. Second, threat actors upload a skill that silently writes .zshenv scripts, guaranteeing root execution when hosts run with sudo.
Microsoft advises never running OpenClaw as root, recommending container isolation instead. Agent Security practitioners echo that guidance, citing classic principle of least privilege. Incident responders report that cleanup often requires full system rebuilds because stealthy persistence hides within numerous dotfiles.
Abusing environment variables or skills converts minor design gaps into catastrophic compromise. In contrast, strict privilege separation thwarts both mechanisms, leading us toward identity considerations.
Misconfiguration And Identity Risks
Identity sprawl magnifies damage once an attacker steals a single agent token. Additionally, many enthusiasts expose the gateway port, believing localhost rules apply across networks. In contrast, scanners easily locate those endpoints, automate exploit, and enumerate credential stores. Consequent privilege escalation often reaches cloud consoles because users reuse identity secrets within agent config. Furthermore, regulators like China’s MIIT now restrict office deployments until strict audits prove Agent Security readiness. Security champions therefore run port scans against internal networks, catching accidental exposures before attackers notice them in the wild.
Weak configurations collapse layered defenses within minutes. Therefore, organizations require a repeatable defensive playbook, explored next.
Defensive Playbook For Organizations
Effective defense starts with disciplined patch management across every OpenClaw host. Moreover, teams must rotate tokens immediately after each public disclosure. Microsoft and OpenClaw both urge isolation through containers, virtual machines, or dedicated workstations. Consequently, install only audited skills and scan them with VirusTotal before enabling. Professionals can deepen expertise by earning the AI Security Level 1 certification. It maps directly to agent hardening practices.
Nevertheless, continuous monitoring remains essential. Recommended queries inspect new shell startup files, abnormal network destinations, and unexpected child processes. Agent Security guidelines suggest sandboxing workloads and forbidding browser sessions on the same host. Teams should also enforce gateway binding rules. They can use a reverse proxy with mutual TLS for zero-trust segmentation.
These controls shrink attack surface and shorten dwell time. Subsequently, leaders must plan for upcoming threats.
Outlook And Next Moves
Threat intelligence firms predict additional CVEs targeting authentication flows and marketplace validation. Moreover, supply-chain attacks will intensify as attackers monetise user trust in skill repositories. Consequently, enterprises will likely tighten agent approval processes, mirroring mobile app store governance. Meanwhile, researchers call for stronger default identity isolation and signed skill manifests. Agent Security advocates expect regulators to demand clearer attestations of exploit response times. Industry groups are drafting open standards for signed extensions and provenance tracking to curb supply-chain abuse.
Future developments will favor prepared defenders. Consequently, remaining vigilant ensures autonomous tools deliver value rather than breaches.
Conclusion
In summary, Agent Security discipline separates productive automation from immediate catastrophe. Moreover, recent case studies prove that decisive patching, isolation, and monitoring neutralize live attacks. Nevertheless, talented adversaries keep probing every runtime, demanding sustained vigilance. Therefore, Agent Security professionals should maintain inventories, enforce least privilege, and track disclosures in real time. Additionally, leaders can reinforce team skills by pursuing the linked certification and embedding its controls into workflows. Consequently, an Agent Security mindset today secures tomorrow’s autonomous enterprise. Finally, share these guidelines across development, operations, and audit teams to strengthen collective resilience.



