AI+ Security Level 1™
AT-2101
Empowering Cybersecurity with AIStart your AI security journey with our all-in-one bundle. Explore core concepts in AI-driven protection, vulnerability management, and intelligent threat response.
Certification Duration: 40 hours (5 Days)
Enroll Now Purchase Exam Buy Instructor-Led Course Certification SchemeWhy This Certification Matters
Comprehensive Learning
Explore AI and cybersecurity integration through Python, machine learning, and threat mitigation to build a strong technical foundation.
Hands-on Approach
Apply concepts in a Capstone Project, solving real-world cybersecurity challenges by leveraging AI tools and practical problem-solving skills.
Cutting-Edge Knowledge
Dive into advanced topics like AI-based authentication and GANs to understand next-gen cybersecurity strategies and innovations.
Boost Strategic Decision-Making with AI Analytics
Master AI models to analyze business data, predict outcomes, and enable more informed, real-time decisions that enhance competitive advantage.
AI-Driven Threat Detection
Learn to detect malware, phishing, and anomalies using machine learning, enhancing your ability to predict and prevent attacks.
Industry Relevance
Stay ahead in cybersecurity by mastering AI applications, making you a valuable asset for future-focused security roles and organizations.
Prerequisites
- Basic Python Programming: Familiarity with loops, functions, and variables.
- Basic Cybersecurity Knowledge: Understanding of CIA triad and common threats (e.g., malware, phishing).
- Basic Machine Learning Concepts: Awareness of fundamental machine learning concepts, not mandatory.
- Basic Networking: Understanding of IP addressing and TCP/IP protocols.
- Linux/Command Line Skills: Ability to navigate and use the CLI effectively.
There are no mandatory prerequisites for certification. Certification is based solely on performance in the examination. However, candidates may choose to prepare through self-study or optional training offered by AI CERTs® Authorized Training Partners (ATPs).
Exam Policies & Integrity
Before your exam, you must accept the AI CERTs® Candidate Agreement. It ensures fairness, transparency, and unbiased certification for all candidates.
View Candidate HandbookPlease review it in advance to understand our exam standards and your responsibilities.
Modules
11
Examination
1
50 MCQs
90 Minutes
Passing Score
70% (35/50)
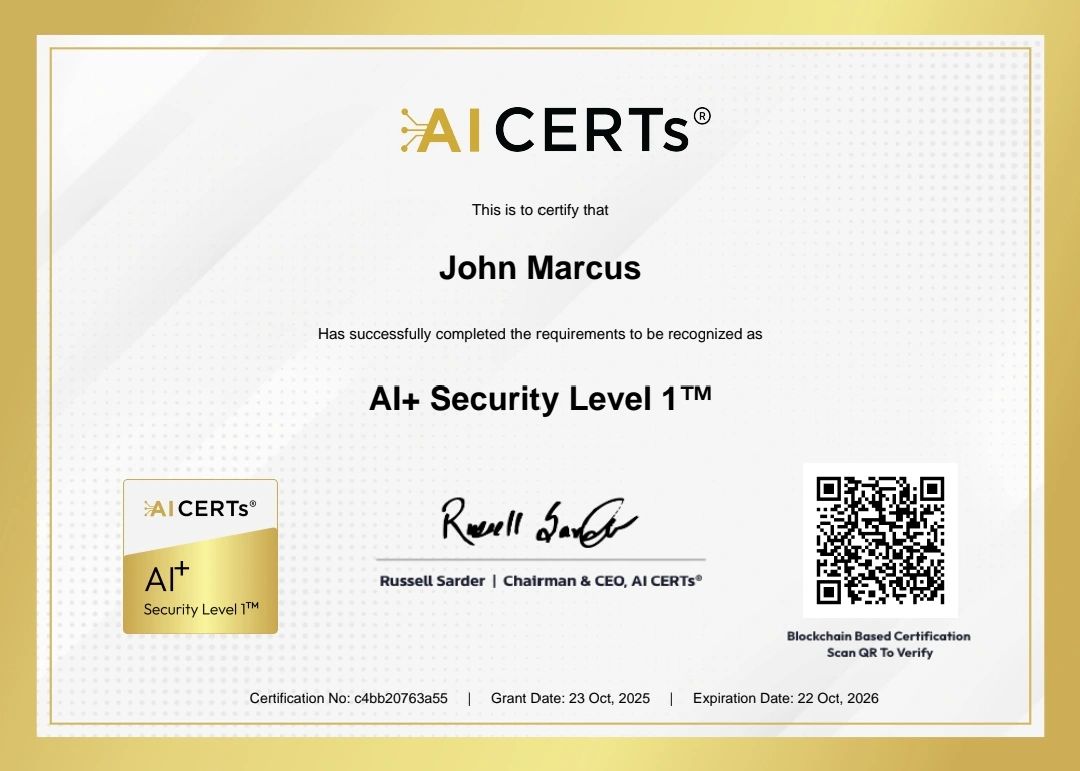
Recertification Requirements
AI CERTs requires recertification every year to keep your certification valid. Notifications will be sent three months before the due date, and candidates must follow the steps in the candidate handbook to complete the process.
Need Help? If you have any questions or need assistance with recertification, please reach out to our support team at support@aicerts.ai
Certification Modules
- 1.1 Definition and Scope of Cybersecurity
- 1.2 Key Cybersecurity Concepts
- 1.3 CIA Triad (Confidentiality, Integrity, Availability)
- 1.4 Cybersecurity Frameworks and Standards (NIST, ISO/IEC27001)
- 1.5 Cyber Security Laws and Regulations (e.g., GDPR, HIPAA)
- 1.6 Importance of Cybersecurity in Modern Enterprises
- 1.7 Careers in Cyber Security
- 2.1 Core OS Functions (Memory Management, Process Management)
- 2.2 User Accounts and Privileges
- 2.3 Access Control Mechanisms (ACLs, DAC, MAC)
- 2.4 OS Security Features and Configurations
- 2.5 Hardening OS Security (Patching, Disabling Unnecessary Services)
- 2.6 Virtualization and Containerization Security Considerations
- 2.7 Secure Boot and Secure Remote Access
- 2.8 OS Vulnerabilities and Mitigations
- 3.1 Network Topologies and Protocols (TCP/IP, OSI Model)
- 3.2 Network Devices and Their Roles (Routers, Switches, Firewalls)
- 3.3 Network Security Devices (Firewalls, IDS/IPS)
- 3.4 Network Segmentation and Zoning
- 3.5 Wireless Network Security (WPA2, Open WEP vulnerabilities)
- 3.6 VPN Technologies and Use Cases
- 3.7 Network Address Translation (NAT)
- 3.8 Basic Network Troubleshooting
- 4.1 Types of Threat Actors (Script Kiddies, Hacktivists, Nation-States)
- 4.2 Threat Hunting Methodologies using AI
- 4.3 AI Tools for Threat Hunting (SIEM, IDS/IPS)
- 4.4 Open-Source Intelligence (OSINT) Techniques
- 4.5 Introduction to Vulnerabilities
- 4.6 Software Development Life Cycle (SDLC) and Security Integration with AI
- 4.7 Zero-Day Attacks and Patch Management Strategies
- 4.8 Vulnerability Scanning Tools and Techniques using AI
- 4.9 Exploiting Vulnerabilities (Hands-on Labs)
- 5.1 An Introduction to AI
- 5.2 Types and Applications of AI
- 5.3 Identifying and Mitigating Risks in Real-Life
- 5.4 Building a Resilient and Adaptive Security Infrastructure with AI
- 5.5 Enhancing Digital Defenses using CSAI
- 5.6 Application of Machine Learning in Cybersecurity
- 5.7 Safeguarding Sensitive Data and Systems Against Diverse Cyber Threats
- 5.8 Threat Intelligence and Threat Hunting Concepts
- 6.1 Introduction to Python Programming
- 6.2 Understanding of Python Libraries
- 6.3 Python Programming Language for Cybersecurity Applications
- 6.4 AI Scripting for Automation in Cybersecurity Tasks
- 6.5 Data Analysis and Manipulation Using Python
- 6.6 Developing Security Tools with Python
- 7.1 Understanding the Application of Machine Learning in Cybersecurity
- 7.2 Anomaly Detection to Behavior Analysis
- 7.3 Dynamic and Proactive Defense using Machine Learning
- 7.4 Utilizing Machine Learning for Email Threat Detection
- 7.5 Enhancing Phishing Detection with AI
- 7.6 Autonomous Identification and Thwarting of Email Threats
- 7.7 Employing Advanced Algorithms and AI in Malware Threat Detection
- 7.8 Identifying, Analyzing, and Mitigating Malicious Software
- 7.9 Enhancing User Authentication with AI Techniques
- 7.10 Penetration Testing with AI
- 8.1 Incident Response Process (Identification, Containment, Eradication, Recovery)
- 8.2 Incident Response Lifecycle
- 8.3 Preparing an Incident Response Plan
- 8.4 Detecting and Analyzing Incidents
- 8.5 Containment, Eradication, and Recovery
- 8.6 Post-Incident Activities
- 8.7 Digital Forensics and Evidence Collection
- 8.8 Disaster Recovery Planning (Backups, Business Continuity)
- 8.9 Penetration Testing and Vulnerability Assessments
- 8.10 Legal and Regulatory Considerations of Security Incidents
- 9.1 Introduction to Open-Source Security Tools
- 9.2 Popular Open Source Security Tools
- 9.3 Benefits and Challenges of Using Open-Source Tools
- 9.4 Implementing Open Source Solutions in Organizations
- 9.5 Community Support and Resources
- 9.6 Network Security Scanning and Vulnerability Detection
- 9.7 Security Information and Event Management (SIEM) Tools (Open-Source options)
- 9.8 Open-Source Packet Filtering Firewalls
- 9.9 Password Hashing and Cracking Tools (Ethical Use)
- 9.10 Open-Source Forensics Tools
- 10.1 Emerging Cyber Threats and Trends
- 10.2 Artificial Intelligence and Machine Learning in Cybersecurity
- 10.3 Blockchain for Security
- 10.4 Internet of Things (IoT) Security
- 10.5 Cloud Security
- 10.6 Quantum Computing and its Impact on Security
- 10.7 Cybersecurity in Critical Infrastructure
- 10.8 Cryptography and Secure Hashing
- 10.9 Cyber Security Awareness and Training for Users
- 10.10 Continuous Security Monitoring and Improvement
- 11.1 Introduction
- 11.2 Use Cases: AI in Cybersecurity
- 11.3 Outcome Presentation
- 1. Understanding AI Agents
- 2. What Are AI Agents
- 3. Key Capabilities of AI Agents in Cyber Security
- 4. Applications and Trends for AI Agents in Cyber Security
- 5. How Does an AI Agent Work
- 6. Core Characteristics of AI Agents
- 7. Types of AI Agents
Tools

CrowdStrike

Flair.ai

ChatGPT

Pluralsight
Exam Objectives
Automation of Security Processes
Learners will develop the ability to automate routine security tasks such as monitoring, logging, and incident response using AI technologies, improving efficiency and accuracy.
Data Privacy and Compliance in AI Security
Learners will understand the importance of data privacy and regulatory compliance when using AI in security, enabling them to develop and implement secure, legally compliant systems.
Threat Detection and Response Using AI
Learners will develop the skills to use AI-powered tools and techniques to detect, analyze, and respond to security threats in real-time
Real-Time Cyberattack Prevention with AI
Learners will acquire the ability to leverage AI to anticipate and prevent cyberattacks before they occur, using predictive models and behavioral analysis.
AI Security Career Advancement – Your Path to Cyber Resilience

Market Demand for AI Security Experts
- The global AI security market is projected to reach $38 billion by 2028, with organisations prioritising AI-driven security measures.
- Studies indicate that cyber security attacks have increased by 300%, making AI security skills crucial for businesses.
- High-Growth Areas: AI Threat Detection, Secure AI Governance, Cyber Risk Mitigation, and AI-Driven Compliance.
- AI security experts are in high demand, making this certification an essential step for professionals in IT, cyber security, and risk management.
Smart Solutions for AI- Powered Credentials

Secure, tamper-proof certifications with blockchain technology and Al integration. Instant verification and custom designs for your brand.


Al-enhanced proctoring for reliable assessments with automated integrity checks and live monitoring. Powering the future of certifications with Al and blockchain.
Discover Your Ideal Role-Based Certifications and Programs!
Not sure which certifications to go for? Take our quick assessment to discover the perfect role-based certifications and programs tailored just for you.
Get CertifiedFrequently Asked Questions
The AI+ Security Level 1™ certification is a foundational course focusing on AI-powered security solutions, including threat detection, automated response, and incident management.
This course is ideal for cybersecurity professionals, network engineers, IT managers, and AI enthusiasts aiming to enhance their knowledge of AI-driven security techniques.
You will learn about AI-based threat detection, machine learning for security automation, AI-driven incident response, and compliance with standards like GDPR, HIPAA, and NIST.
You’ll receive course materials, case studies, project guidance, and access to an online community of learners.
Yes, AI+ Security Level 1™ certification is widely recognized as a benchmark for foundational knowledge in AI-powered security solutions.