
AI CERTS
4 months ago
Quantum Security Migration Demands Deliberate Roadmaps
However, replacing entrenched algorithms like RSA demands careful planning, not a reckless switch. The following guide outlines emerging threats, roadmap steps, ecosystem trends, performance trade-offs, and governance imperatives. Readers gain actionable insights to launch, accelerate, and validate their Quantum Security programs. Moreover, the piece highlights expert quotes, current statistics, and learning resources for a confident transition. Meanwhile, professionals can expand strategic design skills via the AI+ UX Designer™ certification.
Emerging Quantum Threats Today
Harvest-now, decrypt-later attacks already target sensitive archives in finance, health, and defense. Attackers record encrypted sessions today, planning future quantum decryption of RSA or ECC secrets. Furthermore, CISA Director Jen Easterly warned, “It is imperative for all organizations to begin preparing now.” NIST echoed the alert by drafting IR 8547, a transition blueprint for federal and commercial networks. Therefore, Quantum Security implementation must start before cryptographic lifecycles expire. Dustin Moody noted that HQC became a backup algorithm because fallback options increase overall Quantum Security resilience. In contrast, rushing toward unvetted primitives could amplify vulnerabilities and erode trust. These signals confirm the rising threat landscape and the non-negotiable need for proactive defense. Consequently, leaders must adopt a structured migration roadmap to steer complex upgrades.
Structured Migration Roadmap Steps
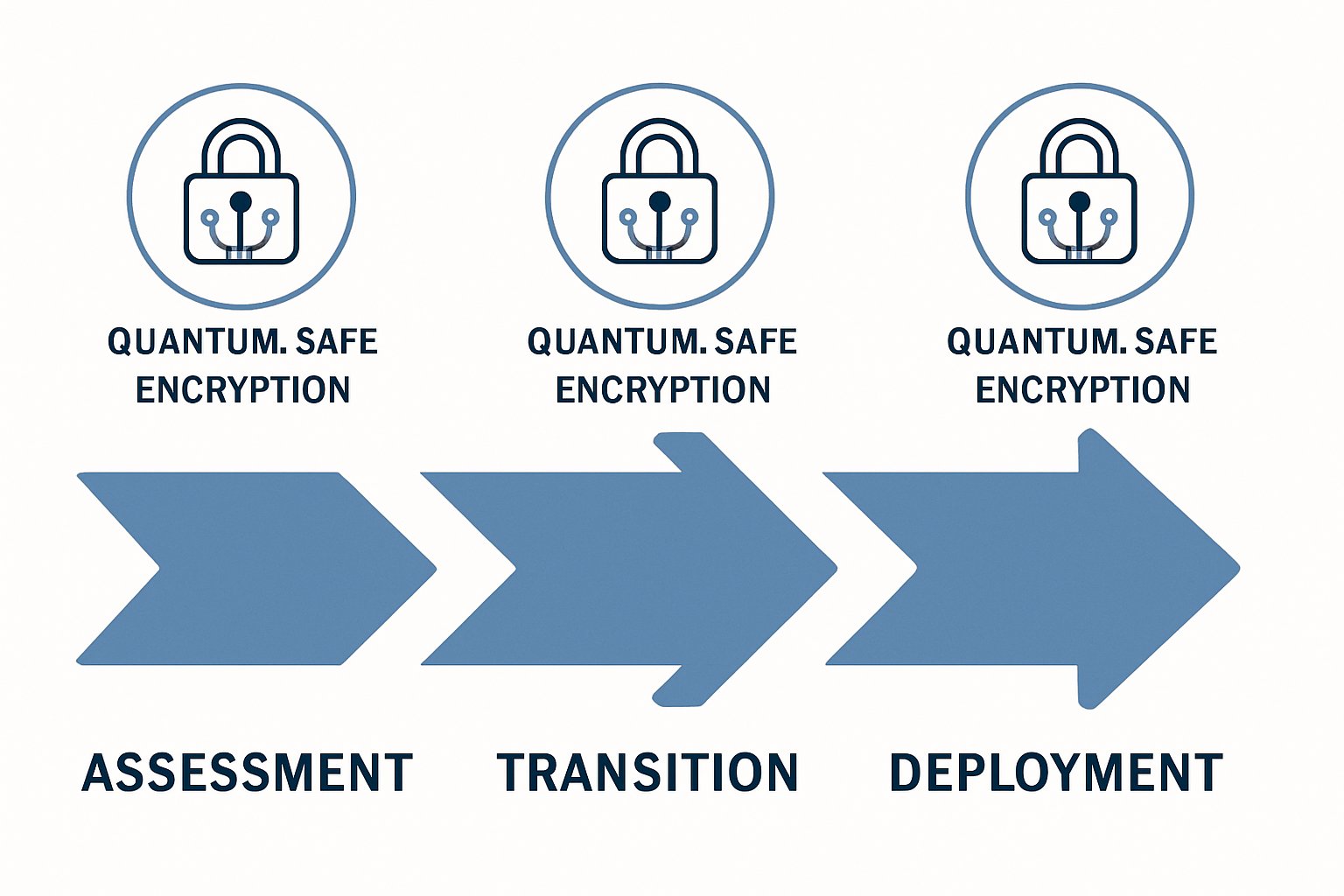
Successful programs follow clear phases: inventory, risk triage, crypto-agility, staged deployment, and verification. NIST, CISA, and NCSC-UK align on this disciplined sequence. Moreover, each phase embeds controls that reduce implementation vulnerabilities before mass rollout. Quantum Security strategists begin with exhaustive asset discovery covering certificates, VPNs, firmware, and embedded devices. Subsequently, teams classify long-lived secrets and prioritize high-impact services for early PQC pilots. During design, engineers bake crypto-agility into software so algorithms can swap without architectural rewrites. Finally, staged deployments use hybrid X25519 + ML-KEM handshakes, allowing rollback if unexpected performance trade-offs appear. Therefore, the roadmap balances speed, reliability, and Quantum Security assurance.
Practical Migration Action Checklist
- Assign an executive owner and publish a Migration charter aligned with enterprise risk appetite.
- Inventory every instance of Cryptography across applications, networks, and supply chains.
- Adopt hybrid PQC key agreements to mitigate algorithmic uncertainties.
- Demand vendor roadmaps that specify hardware support and firmware update windows.
- Establish continuous testing pipelines to detect performance regressions and emerging vulnerabilities before production.
These steps translate lofty standards into concrete engineering actions. Next, understanding adoption trends helps benchmark progress and galvanize sponsorship.
Global Ecosystem Adoption Trends
Cloudflare telemetry shows client browsers embracing PQC hybrids far faster than origin servers. By late 2025, a substantial share of user traffic negotiated ML-KEM pairs, yet only single-digit origins responded. Microsoft, Akamai, and major CAs publish similar roadmaps, underscoring uneven migration momentum. Meanwhile, MarketsandMarkets projects the PQC market will hit USD 2.84 billion by 2030, reflecting soaring demand. Nevertheless, hardware support for emerging Cryptography remains patchy, especially within constrained IoT devices. Security-conscious adopters must therefore pressure suppliers, monitor IETF drafts, and schedule firmware refreshes. These trends reveal progress yet spotlight supply-chain dependencies. Consequently, organizations must weigh performance trade-offs before scaling pilot deployments.
Balancing Performance Trade-offs
Post-quantum keys and ciphertexts are larger, inflating TLS ClientHello packets and sometimes triggering fragmentation. Moreover, CPU cycles increase during ML-KEM operations, stressing mobile and edge hardware. Cloudflare engineers measured median handshake inflation of 3-4 milliseconds, acceptable for most web scenarios. However, high-frequency trading platforms cannot tolerate added latency without optimization. Engineers can compress certificate chains, enable session resumption, or offload Cryptography to hardware accelerators. Hybrid handshakes limit regression while still delivering Quantum Security protections. In contrast, a single-algorithm switch exposes organizations to algorithmic surprises, similar to the 2022 SIKE collapse. These insights demonstrate that measured tuning can offset performance trade-offs. Subsequently, robust governance ensures tuning changes do not introduce fresh vulnerabilities.
Robust Governance And Testing
Governance frameworks anchor technical work to risk management objectives. NIST advises mapping PQC milestones to existing cybersecurity controls like CSF and ISO 27001. Additionally, boards should demand periodic Quantum Security status reports and allocate sustained funding. Test regimes must include fuzzing, side-channel probes, cross-vendor interoperability, and adversarial packet injection. Independent reviewers caught critical vulnerabilities in early PQC libraries, validating the need for multiple eyes. Therefore, continuous integration pipelines should fail builds when cryptographic linting detects misconfiguration. These governance practices sustain trust and minimize operational surprises. Meanwhile, forward-looking vision keeps teams engaged with evolving standards and vendor updates.
Future Outlook And Actions
National timelines converge around 2033-2035 for complete post-quantum rollouts, yet early movers gain defensive advantage. Moreover, market forecasts predict multi-billion spending on consulting, hardware, and managed Cryptography services. Organizations that operationalize Quantum Security today can negotiate favorable pricing and shape vendor roadmaps. Professionals should therefore cultivate cross-disciplinary skills in engineering, compliance, and user experience. They can validate expertise through the AI+ UX Designer™ certification. The program highlights secure, intuitive design for complex cryptographic applications. Consequently, certified leaders bridge technical and human dimensions during Migration. These outlook insights underline the urgency of disciplined action. The final section distills major lessons and invites decisive steps.
Quantum threats are no longer distant abstractions. Standards, vendor roadmaps, and government mandates now align behind a deliberate PQC Migration agenda. However, success requires inventory, crypto-agility, staged deployment, and relentless testing. Balanced performance Trade-offs and vigilant governance prevent new vulnerabilities from eclipsing gains. Therefore, organizations should launch or accelerate Quantum Security initiatives without delay. Explore emerging standards, engage suppliers, and mandate hybrid Cryptography in upcoming releases. Finally, advance your expertise and influence by pursuing the highlighted certification and sharing progress across your ecosystem.



