
AI CERTS
2 hours ago
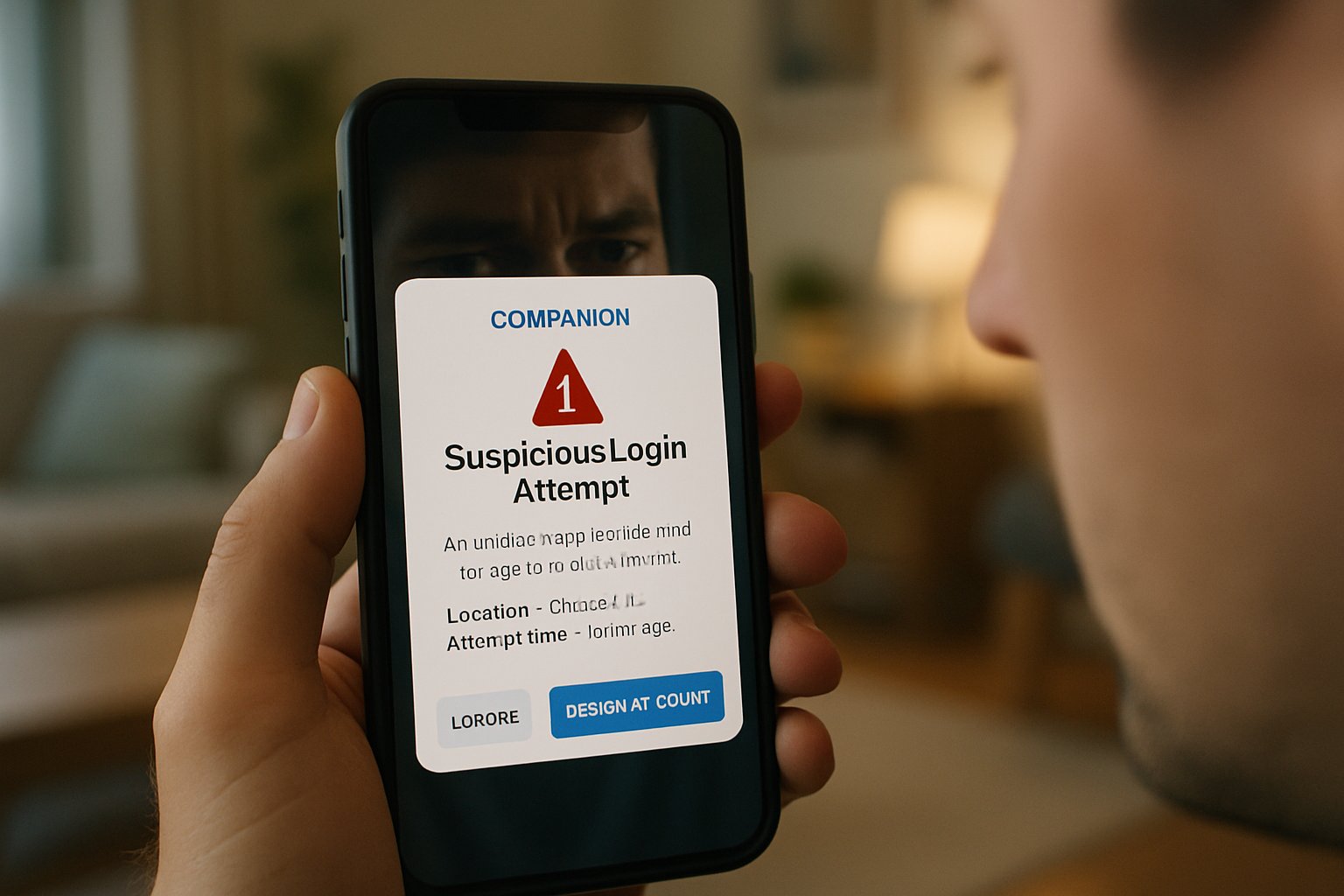
Privacy Security Breach Confusion: Aura And Companion App Risks
Moreover, regulators warn that unchecked data exposure can amplify fraud losses. This article dissects the confusion, details the technical evidence, and offers actionable mitigation. Readers will find expert quotes, market context, and certification resources.
Confusion Clouds Recent Breaches
Social posts in March suggested Aura leaked 900,000 records. However, no regulator or mainstream outlet confirmed the claim. Researchers instead documented attackers abusing AuraInspector to scrape misconfigured Salesforce guest profiles. ShinyHunters reportedly led that campaign. Meanwhile, identity-protection users worried about a different Privacy Security Breach entirely. The identical word “Aura” fed the online confusion. Nevertheless, security teams must separate unverified chatter from documented exploits.
These events teach one clear lesson. Word collisions can mask true risk. However, deeper analysis reveals distinct attack chains.
Identity Services Market Pulse
The FTC logged 1.1 million identity-theft reports in 2024. Furthermore, The Business Research Company pegs the protection market at $16.26 billion for 2026. Aura, by its last public filing, claimed around $150 million ARR. Although figures differ across aggregators, growth remains brisk. Consumers buy monitoring, credit alerts, and insurance. Yet each subscription cannot stop every Privacy Security Breach. Services mainly shorten detection windows and simplify recovery.
Market highlights underline accelerating demand. However, adoption without education still leaves gaps.
Companion Apps Weak Points
Companion apps control smart bulbs, trackers, and even AI girlfriends. Academic work titled “Beware of the App!” found half the studied apps lacked proper encryption. Additionally, CVE-2024-31318 showed Android pairing APIs could be bypassed. In contrast, manufacturers tout convenience and rapid updates. Unfortunately, weak authentication often leads to silent data exposure. Malicious actors exploit overly broad permissions or unencrypted channels, then bundle stolen profiles for phishing.
- 50% of reviewed apps missed adequate encryption.
- 38% of sampled devices relied on those insecure apps.
- Android patched a 7.8-severity companion vulnerability in 2024.
Developers must treat every pairing request as hostile. Nonetheless, code audits remain sporadic across consumer brands.
Encryption failures and lax permissions fuel breaches. Consequently, ignoring companion security invites another Privacy Security Breach.
Real Exploits, Hard Numbers
Mandiant’s Charles Carmakal confirmed attackers modified AuraInspector for automated scans. Therefore, hundreds of Salesforce Experience Cloud portals leaked contact data. Salesforce stated misconfigurations, not platform flaws, enabled the theft. Moreover, logs showed scanning did not always equal compromise. Meanwhile, AI girlfriends apps experienced scraping events that exposed chat transcripts. Each incident contributed to mounting data exposure counts across underground forums.
Key statistics continue to climb. Nevertheless, transparent metrics help leaders allocate defense budgets.
Mitigation Strategies And Certifications
Organizations should first inventory every public endpoint. Subsequently, enforce least-privilege on guest profiles and companion APIs. Multi-factor authentication, strong encryption, and continuous monitoring reduce Privacy Security Breach likelihood. Consumers, likewise, can freeze credit files and watch dark-web alerts. Professionals can enhance their expertise with the AI+ Developer™ certification. The course covers secure coding, threat modeling, and incident response fundamentals.
Sensible controls shrink the attack surface. However, ongoing education ensures defenses evolve with threats.
Future Outlook And Recommendations
Identity-protection services will integrate richer telemetry. Additionally, platform vendors plan default encryption for companion traffic. Regulatory action may mandate breach disclosure within days. In contrast, attackers automate scanning faster than many firms patch. AI girlfriends will gain safer trust frameworks, yet personal settings still matter. Strategic investment in audits, staff training, and verifiable metrics can avert the next Privacy Security Breach.
Tomorrow’s landscape demands vigilance and agility. Therefore, leaders must align budget, policy, and culture now.
The converging stories show different roots but similar consequences. Moreover, clear facts dispel fear and guide smart action. Stay informed, review settings, and pursue advanced training to guard against every emerging Privacy Security Breach.



