
AI CERTS
1 hour ago
DarkSword and iOS: Mobile Cybersecurity Threats Escalate in 2026
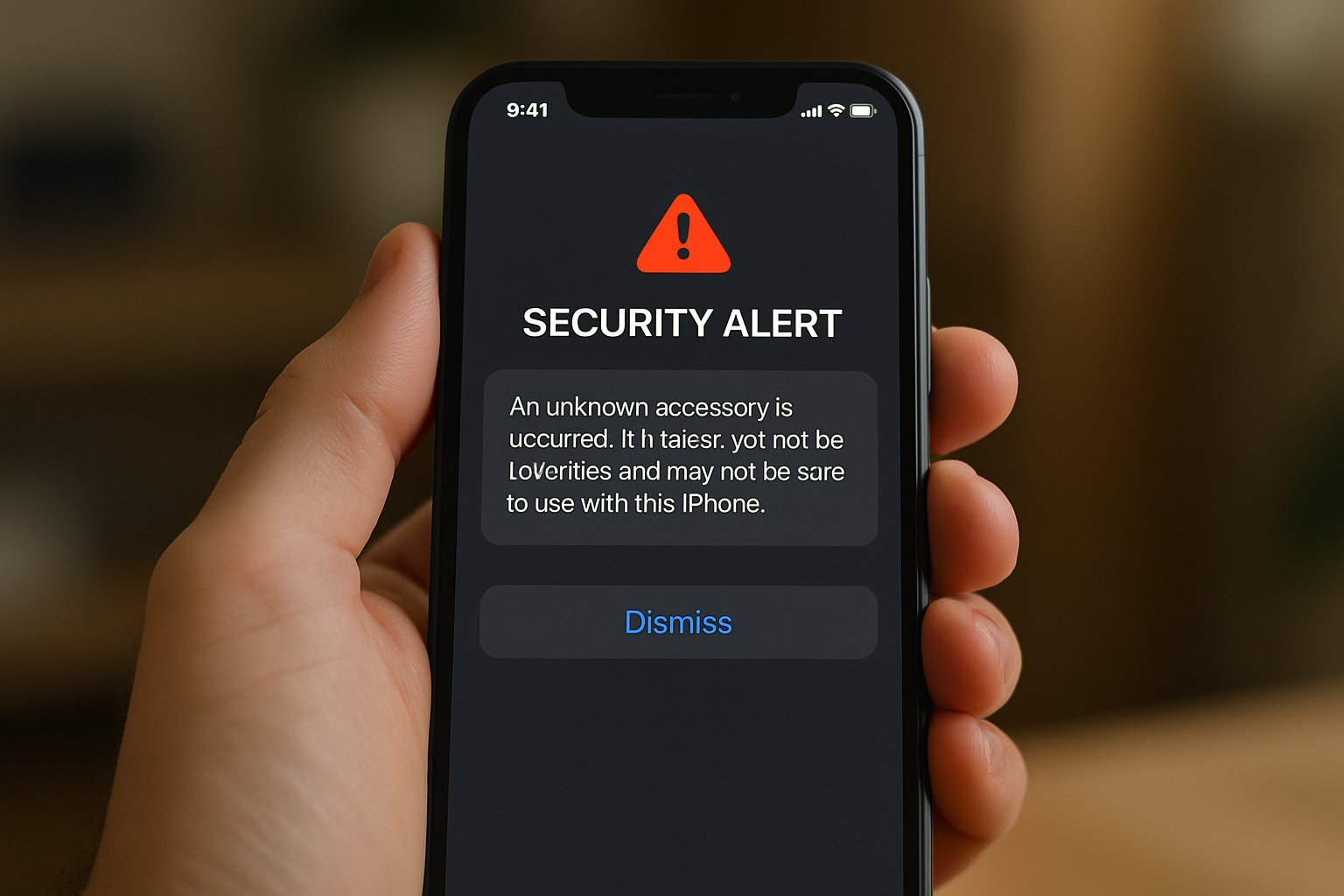
However, many devices remain unpatched, creating a fertile hunting ground for adversaries. DarkSword weaponizes web pages, silently compromising iPhones that merely load an infected site. Moreover, in-memory implants scrape credentials, messages, and health data before vanishing on reboot. Subsequently, we outline policy implications and certification pathways that elevate defensive readiness.
Evolving Mobile Cybersecurity Threats
Attacks that once demanded nation-state budgets now circulate cheaply through exploit brokers. Consequently, defenders observe a sharp rise in turnkey kits focused on smartphones. The toolkit exemplifies this trend, pairing polished code with commoditized infrastructure. In contrast, previous iOS spyware often lacked wide device compatibility.
Now, operators can rent a full chain that spans browser, sandbox, and kernel layers. Therefore, Mobile Cybersecurity Threats have escalated beyond targeted espionage into broad corporate risk categories. Justin Albrecht at Lookout warns that resale markets lower the entry barrier further. These dynamics confirm an accelerating threat curve. Meanwhile, understanding the precise exploit mechanics clarifies defensive priorities.
DarkSword Attack Mechanics Explained
Researchers mapped a four-stage sequence that starts within WebKit’s JavaScriptCore engine. Firstly, malicious code triggers CVE-2025-31277, granting remote code execution in the browser context. Secondly, a sandbox escape leverages CVE-2025-43529 to reach broader system APIs. Furthermore, the chain then escalates privileges in the kernel, installing a fileless implant. That implant dumps passwords, keychain items, and messaging databases from iPhones in seconds.
Nevertheless, persistence is avoided to reduce forensic traces. DarkSword abandons the device on reboot, yet the underlying vulnerability remains exploitable until patched. Consequently, traditional antivirus tools rarely record artifacts, complicating incident response. Such insight reinforces Mobile Cybersecurity Threats preparedness across blue teams. Subsequently, we examine the real-world impact of that stealth exfiltration.
Stealth Data Exfiltration Impact
Once privileged, DarkSword siphons vast personal archives to remote command servers. Examples include wallet keys, health metrics, and confidential chats. Moreover, iVerify captured implants extracting entire Signal databases despite sealed iOS backups. This behavior mirrors modern iOS spyware observed in previous Pegasus incidents. Investigators classify the implant sequence as advanced iOS spyware due to its depth of access. Furthermore, victims rarely notice indicators because network traffic appears as regular HTTPS sessions.
Researchers noted exfiltration periods seldom last more than five minutes, minimizing discovery windows. Therefore, Mobile Cybersecurity Threats now include high tempo smash-and-grab models that evade mobile EDR. These findings underline how speed substitutes for persistence. Consequently, we next quantify devices still awaiting patches.
At-Risk Device Populations Map
Apple telemetry shows roughly 25 percent of active iPhones still operate on iOS 18. In contrast, corporate fleets often lag further because of testing requirements. Wired calculated that hundreds of millions could remain vulnerable, though true infection numbers stay unknown. Moreover, GTIG observed DarkSword infrastructure filtering traffic from Ukraine, Turkey, and Malaysia.
Consequently, geographic targeting complicates global patch management strategies. Each unpatched device presents a rolling vulnerability until Apple security updates are applied. Mobile Cybersecurity Threats therefore scale with deployment inertia, not attacker resources alone. These numbers stress the urgency of rapid update cycles. Subsequently, attention turns to actionable mitigation steps.
Practical Mitigation Steps Now
Patching remains the single most effective defense. Therefore, organizations should adopt a layered response plan described below.
- Update to iOS 26.3.1 or 18.7.6 emergency release within 24 hours.
- Enable Lockdown Mode for high-risk teams and journalists.
- Reboot devices daily until patches land, clearing transient implants.
- Deploy mobile EDR to monitor outbound anomalies linked to malicious domains.
- Train staff to identify watering-hole lures, reinforcing awareness of Mobile Cybersecurity Threats.
Additionally, companies should integrate threat intelligence feeds from GTIG and iVerify. Professionals can enhance their expertise with the AI Security Specialist™ certification. That program covers exploit diagnostics, mobile forensics, and incident triage skills. Consequently, trained analysts detect abnormal telemetry faster and coordinate swift containment. These steps shrink exposure windows substantially. Meanwhile, broader policy factors still influence long-term risk. Patch adoption metrics should inform board dashboards tracking outstanding vulnerability debt. Effective hygiene neutralizes most attack attempts. Subsequently, we explore regulatory and market consequences.
Policy And Market Ramifications
Government regulators increasingly scrutinize commercial exploit brokers after consecutive leaks. Moreover, revelations about DarkSword and earlier Coruna emphasize uncontrolled proliferation risks. Lawmakers debate export controls that mirror existing arms regulations. In contrast, civil society groups argue users deserve faster vendor patch pledges. Industry alliances also form to share Mobile Cybersecurity Threats telemetry across carriers and handset makers.
Lookout notes that standardizing payout models for vulnerability disclosures would deter black-market sales. Nevertheless, consensus remains elusive. These debates will shape resource allocation over the next budget cycles. Consequently, strategic plans must anticipate shifting compliance landscapes. Next, we outline forward defense priorities to stay ahead.
Future Strategic Defense Priorities
Security leaders expect exploit kits to iterate rapidly through 2027. Therefore, zero-trust architecture should extend to all mobile endpoints. Threat hunting teams must baseline normal iPhones traffic with machine-learning algorithms. Additionally, continuous red teaming against simulated iOS spyware provides early warning on detection gaps. Quarterly exercises should rehearse crisis communications around Mobile Cybersecurity Threats impacting executives. Moreover, investing in RASP for mobile apps blocks malicious JavaScript payloads at runtime. Organizations ought to treat every untested update window as a standing vulnerability assumption. These forward measures nurture adaptive resilience. Consequently, teams will respond with greater speed and confidence.
DarkSword underscores how swiftly web exploits can compromise trusted handsets. Researchers traced a full chain, from browser bug to kernel command, exfiltrating prized data. Millions of iPhones remain patch-eligible yet exposed. However, prompt updates, Lockdown Mode, and disciplined monitoring drastically lower risk. Consequently, organizations that internalize these lessons will tame escalating Mobile Cybersecurity Threats. Moreover, professionals should pursue continuous education to stay ahead of attackers. The AI Security Specialist™ credential deepens exploit analysis skills and signals leadership commitment. Act now, patch systems, and elevate team expertise before the next toolkit emerges.



