
AI CERTS
3 hours ago
Curl Ends Bounty Citing AI Generated Slop Surge
However, the shift signals broader tension between automation enthusiasts and maintainers battling mounting developer friction. This article unpacks what happened, why AI Generated Slop overwhelmed cURL, and what the industry tries next. Furthermore, we explore metrics, community reactions, and potential disclosure models that may restore balance.
Along the way, you will see how slop reports erode trust and burn precious volunteer hours. Meanwhile, commercial platforms scramble to layer machine learning filters on the mess they helped create. Professionals seeking sharper writing can pursue the AI Writer™ certification for structured guidance. Let’s dive into the data.
Why Curl Finally Withdrew
Curl’s bounty began in 2019 and rewarded 87 confirmed flaws worth over $100,000 before collapse. Nevertheless, valid reports dwindled as AI agents learned to churn plausible prose without real proof. By mid-2025 less than five percent of submissions survived triage, according to Stenberg’s public spreadsheets. Moreover, roughly twenty percent were branded AI Generated Slop, a phrase that soon defined the crisis. In contrast, each bogus ticket still demanded manual reproduction steps, code reading, and diplomatic replies.
Consequently, developer friction soared and volunteers lost weekends verifying phantom crashes. Stenberg finally pulled the plug via GitHub pull request 20312 and an unflinching blog post on 26 January 2026. He wrote that slop reports ‘hamper our will to live,’ underscoring the human cost behind statistical charts. These events reveal why trust evaporated. However, understanding the slop surge magnitude clarifies the policy shift.
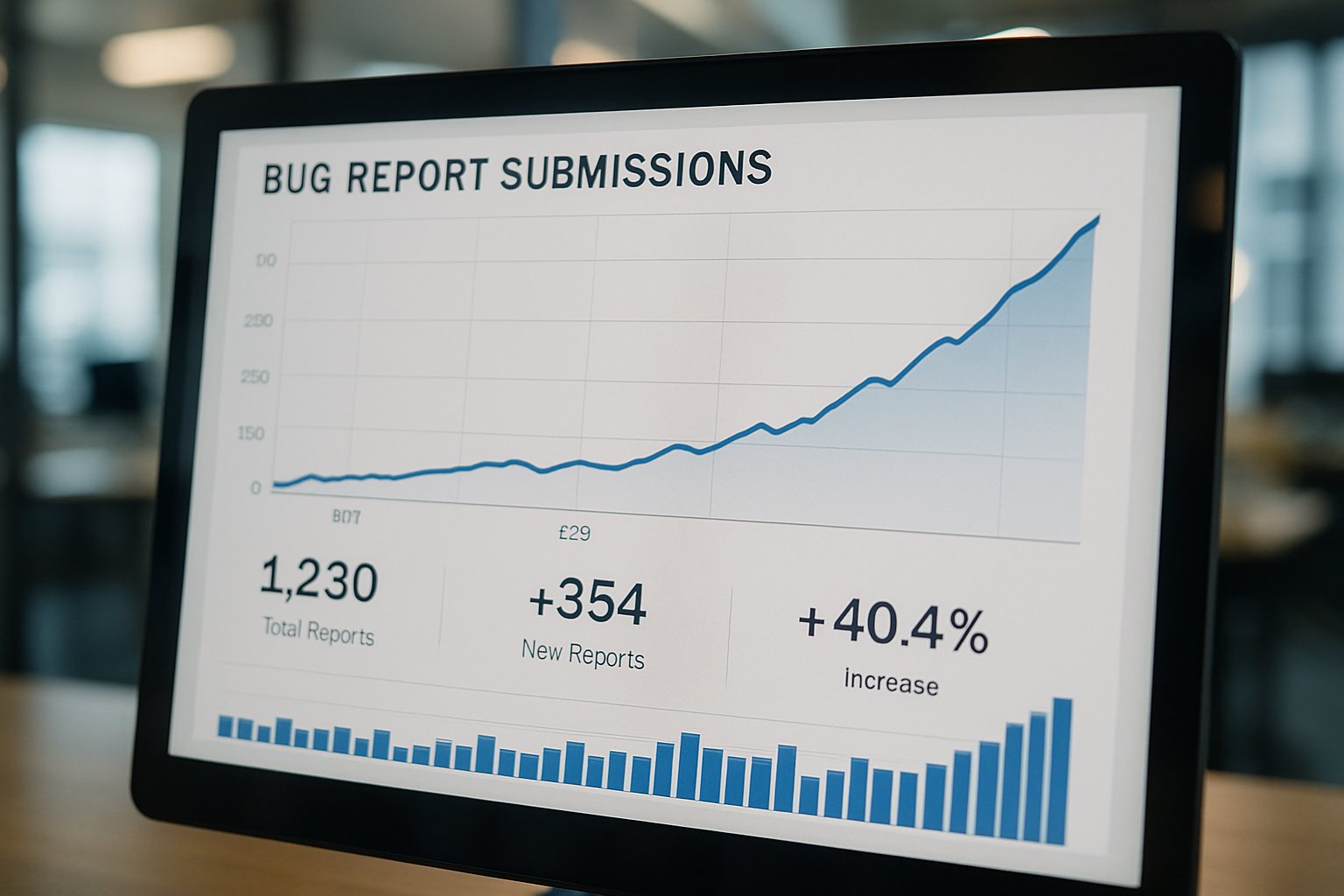
Scale Of Slop Surge
Stenberg’s logs show two security submissions weekly during 2025; only one in twenty proved real. Additionally, one dramatic burst delivered seven HackerOne tickets within sixteen hours, none authentic. Meanwhile, January 2026 alone produced twenty new issues already tagged AI Generated Slop. Those volumes battered the seven-person security roster that guards code used by billions. Consequently, backlog triage time ballooned, and response latency risked public zero-day exposure.
HackerOne staff acknowledged similar waves across other open-source projects and promised forthcoming AI filters. Nevertheless, cURL declined to wait for external tooling and instead dismantled its bug bounty. These raw numbers illustrate why scale, not malice, made the system unsustainable. Subsequently, we examine hard metrics that expose the declining signal-to-noise ratio.
Key Metrics Quick Recap
Quantitative evidence grounds the debate. Therefore, the following figures contextualize the decision.
- Valid vulnerability rate dropped below five percent during 2025.
- Twenty percent of all submissions were flagged as slop reports that year.
- Total rewards paid exceeded one hundred thousand dollars since 2019.
- Seven fake issues arrived within sixteen hours, stressing on-call staff.
- Security team size remained roughly seven volunteer engineers.
- AI Generated Slop phrase appeared in project security.txt as a deterrent to spammers.
Collectively, these data points chart a pattern of overwhelming noise. However, raw numbers tell only part of the human story that follows.
Impacts On Code Maintainers
Triage fatigue bred profound developer friction among volunteers who once celebrated every genuine find. Moreover, misclassified tickets forced context switching that scattered focus across weeks of patch development. Stenberg wrote that the mental toll ‘hampered our will to live,’ framing a stark health warning. In contrast, bounty hunters invested only minutes to paste AI Generated Slop into HackerOne forms.
Consequently, power dynamics shifted and resentment toward both bounty culture and platform friction intensified. Maintainers feared burnout more than undiscovered bugs, a troubling but rational calculus. These sentiments reveal why community goodwill eroded quickly. Subsequently, the wider security ecosystem began searching for systemic countermeasures.
Broader Industry Response Moves
Commercial platforms recognise the pattern and are pivoting fast. For example, HackerOne is beta-testing AI classifiers that auto-close obvious AI Generated Slop. Additionally, OpenSSF discusses proof-of-work gates that raise the cost of automated slop reports. Anthropic and OpenAI pitch safer agent toolkits that embed self-checking routines before filing disclosures. Meanwhile, some maintainers introduce reputation thresholds or require video demonstrations before accepting any bug bounty claim.
These defenses hope to reduce friction without deterring legitimate researchers who still need feedback loops. Nevertheless, experts caution that determined spammers will adapt rapidly. Therefore, layered mitigations will likely become the norm. These shifts demonstrate a market chasing balance between openness and AI Generated Slop mitigation. In contrast, alternatives beyond bounties deserve attention.
Exploring Alternatives And Tradeoffs
Removing cash does not automatically remove noise, according to early February data from Stenberg. Consequently, cURL now relies on GitHub’s private vulnerability channel that hides reports until validated. Some projects experiment with invite-only disclosure lists that favour trusted researchers over first-timers. Moreover, corporate sponsors sometimes pay external audits instead of running a public bug bounty.
Critics argue that dropping rewards discourages newcomers, reducing diversity and long-tail coverage. Supporters counter that lower developer friction offsets any dip in vulnerability yield. Nevertheless, no consensus exists on an optimal mix of incentives and safeguards. These debates set the stage for new disclosure designs. Subsequently, we consider possible future models emerging from those discussions.
Possible Future Disclosure Models
Experts foresee hybrid schemes that blend small rewards with escalating proof requirements. For instance, tokens or deposits refunded upon verified impact could deter frivolous slop reports. Furthermore, maintainers might demand machine-readable exploit scripts that automated pipelines can run quickly. Some suggest delegated triage vendors that shield volunteers from first-contact friction. Meanwhile, AI detectors scoring narrative originality could filter obvious AI Generated Slop before humans review.
OpenSSF plans pilot programs to test such guardrails across popular libraries. Consequently, evidence gathered in 2026 will shape global best practices in 2027. These possibilities indicate that disclosure workflow remains an active research frontier. Nevertheless, practitioners need up-to-date communication skills to navigate whichever model prevails. Professionals may hone reporting clarity via the AI Writer™ certification, improving signal.
Curl’s retreat from rewards underscores a pivotal security inflection point. AI Generated Slop flooded intake channels, slashed true-positive rates, and ignited developer friction. However, the retreat is hardly the final word on collaborative vulnerability hunting. Platforms, standard bodies, and maintainers are iterating toward layered controls that preserve collaboration without burnout.
Consequently, watchers should monitor upcoming pilot programs and post-shutdown metrics to judge effectiveness. Meanwhile, security writers must craft tighter, reproducible submissions to keep their voice respected. Adopt disciplined communication practices today by earning the AI Writer™ certification and lead the next disclosure era.



