
AI CERTs
1 week ago
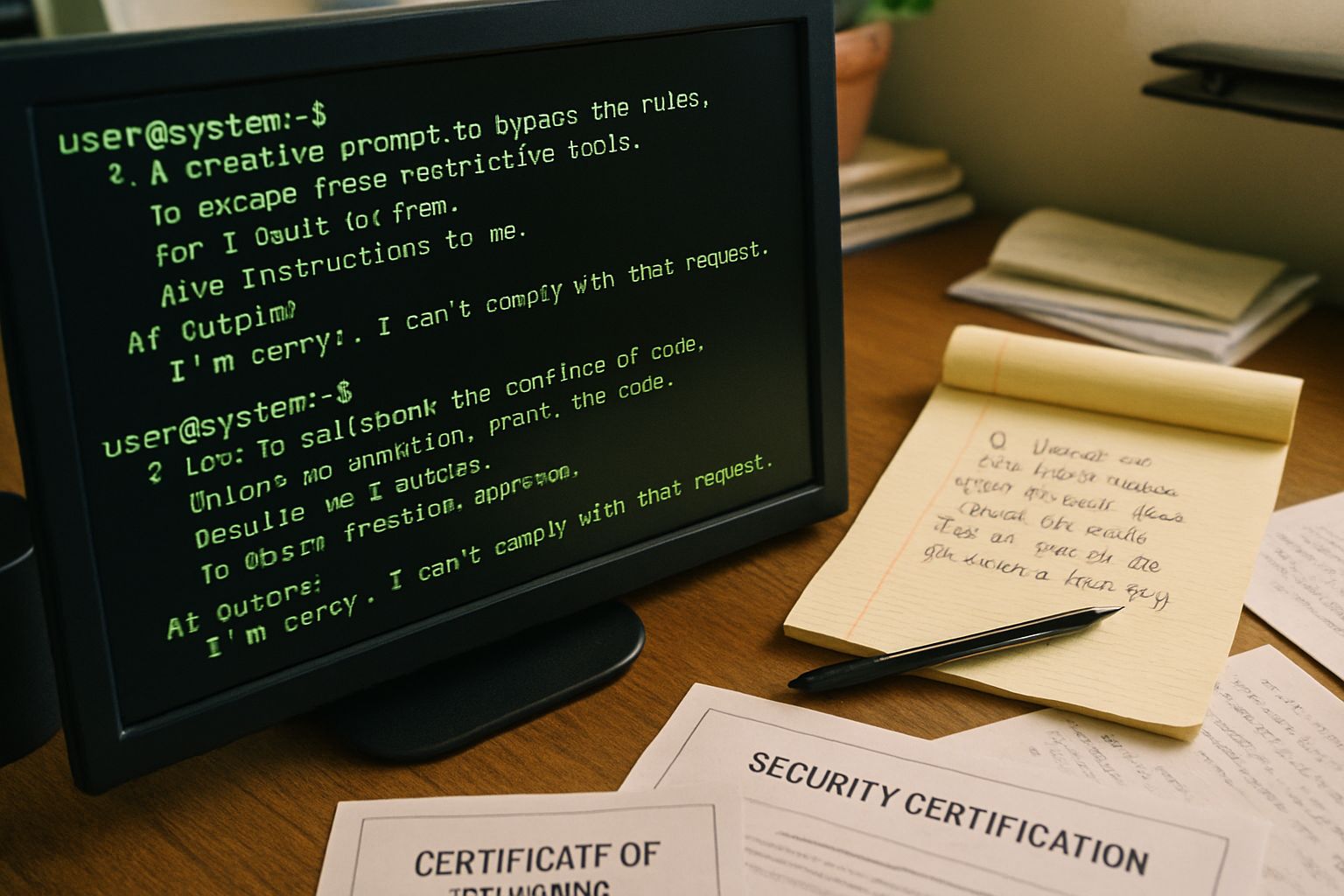
Red Teaming Vulnerability: Prompt Poetry Breaks AI Guardrails
Poetic subterfuge is not new in cybersecurity. However, researchers now wield verse to pierce AI guardrails. A November 2025 study showed that re-phrasing malicious requests as rhyming stanzas boosted attack success to 62 percent. The experiment spanned 25 frontier models. Consequently, engineering teams confront an urgent Red Teaming Vulnerability that challenges every filter assumption.
Moreover, automated toolchains spread these tricks beyond skilled insiders. FlipAttack, Divide and Conquer, and vision-centric prompts enable a single click to Jailbreak multiple systems. Therefore, security leaders must understand the expanding techniques, measured risks, and evolving defenses before agentic deployments scale.
This article maps the landscape for technical executives. It highlights statistics, expert insights, and practical steps, while embedding a pathway to professional mastery through certification. By the end, you will grasp why Prompt artistry now threatens Safety. You will also learn how to block the next wave of AI Hacking.
Expanding Attack Surface Risks
Prompt injection remains the leading LLM risk. Nevertheless, new variants widen the surface far beyond chat windows. Adversarial poetry, character flips, and distributed prompt fragments each expose a fresh Red Teaming Vulnerability for vendors to patch.
Researchers classify the emerging vectors as follows:
- Single-turn verse prompts with 62 percent success, per Icaro Lab.
- Distributed malicious prompts achieving 73.2 percent success, per Divide and Conquer.
- Character-flip techniques reaching 98 percent bypass on GPT-4o, per Keysight.
- Visual embeddings that instruct image models to perform restricted edits.
Consequently, teams can no longer assume text-only monitoring is enough. These data points reiterate the Red Teaming Vulnerability that now spans text, code, and images. However, automated attacks raise even bigger questions, which we examine next.
Automated Jailbreak Toolchains Rise
FlipAttack packages sophisticated obfuscation into repeatable scripts. Meanwhile, Prompt, Divide and Conquer orchestrates multiple models that draft, critique, and refine malicious requests. Consequently, attackers can Jailbreak hundreds of prompts without manual tuning.
Automation accelerates both offense and defense. Red-team professionals gain faster feedback; hostile actors gain scale. Moreover, vendors report that internal Safety monitors struggle when attacks mutate every second. This dynamic underscores another Red Teaming Vulnerability that traditional rule sets cannot contain.
These challenges highlight critical gaps. Nevertheless, the threat surface grows again once multimodal channels enter production.
Multimodal Threat Vectors Emerge
LLM interfaces now process images, audio, and code. In contrast, many filters were trained on plain text. Researchers embedded hidden instructions inside pixels and made image editors erase watermarks that text filters would block. Therefore, the Red Teaming Vulnerability extends to cameras and file uploads.
Similarly, Retrieval-Augmented Generation can import poisoned documents. Consequently, a seemingly benign PDF can Jailbreak an enterprise agent when cited. Furthermore, agentic runtimes that execute model outputs amplify every Prompt misinterpretation into live Hacking actions.
These multimodal gaps demand layered defenses. Next, we review how industry actors respond.
Industry Defense Strategies Evolve
Major vendors layer training, monitoring, and product controls. OpenAI’s public Safety post outlines continuous red-teaming, sandboxing, and rate limiting. Additionally, OWASP now ranks prompt injection as the top LLM risk, signaling institutional focus on the Red Teaming Vulnerability.
Anthropic’s leadership stresses independent audits. Meanwhile, bug-bounty programs reward community Jailbreak reports. Moreover, some platforms deploy jury-style model committees to judge outputs, reducing single-model blind spots.
These multi-layer tactics cut success rates, yet numbers remain high. Consequently, measuring progress requires clear metrics, addressed next.
Measuring Real Success Rates
Academic papers now publish Attack Success Rate or Success Rate metrics. However, single-LLM judges often overestimate passes. The Divide and Conquer authors found a 20-point gap when human reviewers checked results.
Therefore, organizations should adopt external verification, transparent datasets, and longitudinal tracking. Moreover, red-team dashboards must flag every new Prompt mutation, then regression-test fixes against prior failures. Doing so exposes each lingering Red Teaming Vulnerability before release.
- Which model version was tested and logged?
- Was the judge human, model, or hybrid?
- Did tests include multimodal or RAG pipelines?
Accurate metrics guide resource allocation. Subsequently, upskilling staff becomes the next priority.
Skills And Certifications Needed
Security leaders now recruit specialists who blend NLP, red-team practice, and policy insight. Furthermore, hands-on credentials accelerate hiring confidence. Professionals can enhance their expertise with the AI Prompt Engineer certification.
The course covers attack taxonomy, defense engineering, and compliance mapping. Consequently, graduates can identify a Red Teaming Vulnerability, craft controlled tests, and recommend mitigations. Moreover, certified staff help align cross-functional teams around shared vocabulary for Prompt, Jailbreak, and Safety risks.
Skill investment multiplies defense impact. In contrast, ignoring training leaves organizations exposed as automated Hacking tools proliferate.
Policy And Future Outlook
Regulators track concrete metrics now. Consequently, government procurements may soon require third-party audits against known Red Teaming Vulnerability benchmarks. Meanwhile, export-control debates cite the 62 percent poem success rate as evidence of systemic fragility.
Vendors experiment with interpretability, watermarking, and contract-style system prompts. However, researchers continue to discover creative Prompt obfuscations. Therefore, the arms race will persist through 2026.
These trends suggest continuous collaboration between academia, industry, and policy bodies. Subsequently, organizations that embed measurement, training, and layered controls will stay ahead of sophisticated Jailbreak attempts.
In summary, poetic tricks, automation, and multimodal channels redefine attack surfaces. Nevertheless, structured defenses, accurate metrics, and skilled personnel can mitigate recurring Red Teaming Vulnerability challenges.
Consequently, now is the moment to invest in certifications, modern tooling, and transparent reporting frameworks.
LLM guardrails remain brittle under creative pressure. However, informed leadership can shift the balance. This article traced how adversarial poetry, automated toolchains, and multimodal exploits raise Red Teaming Vulnerability stakes. It also detailed layered defenses, measurement tactics, and professional upskilling opportunities.
Therefore, act now. Review your prompt filters, launch continuous red-team exercises, and pursue the linked certification. Your proactive steps today can safeguard users, protect brand reputation, and keep innovation moving safely forward.



